In just over nine months, Zoom has gone from a convenient videoconferencing tool into a household brand name. As business travel, events, and offices around the globe shut down rapidly due to the COVID-19 pandemic, Zoom's suite of videoconferencing functions have provided an essential lifeline that have allowed everyone from educators to CEOs to late-night talk show hosts continue to connect with peers, customers, students, and friends and family. The variety of users who need to host a secure Zoom meeting these days numbers in the millions, a remarkable rise for the company.
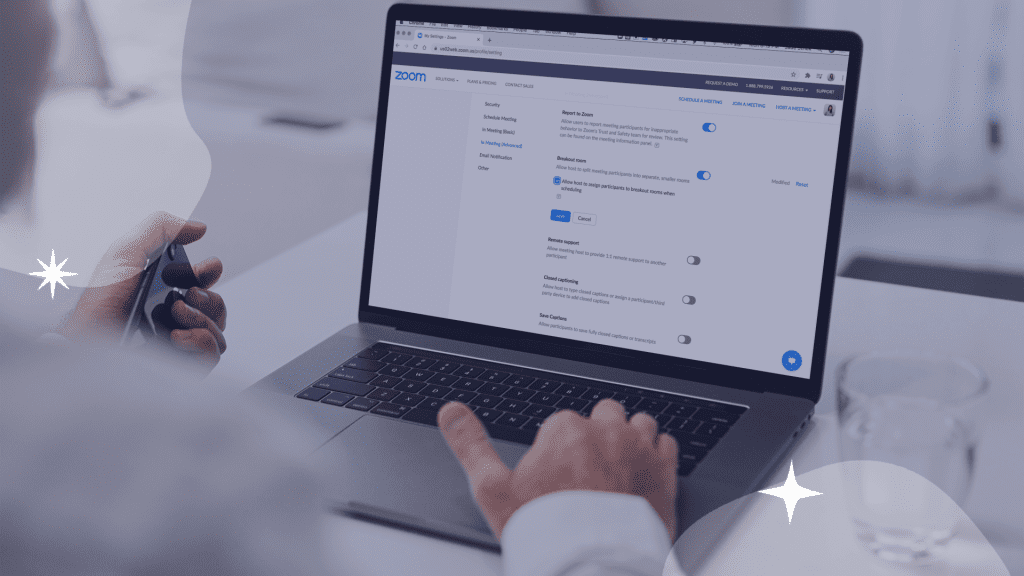
However, while Zoom has made significant improvements to security features since the spring, keeping Zoom meetings secure and uninterrupted still requires some careful use of privacy and security features. Security issues have always been a part of videoconferencing apps, but the widespread adoption of Zoom puts a particular spotlight on some of the more notable flaws that have been exposed as more and more of the world have adopted the platform.
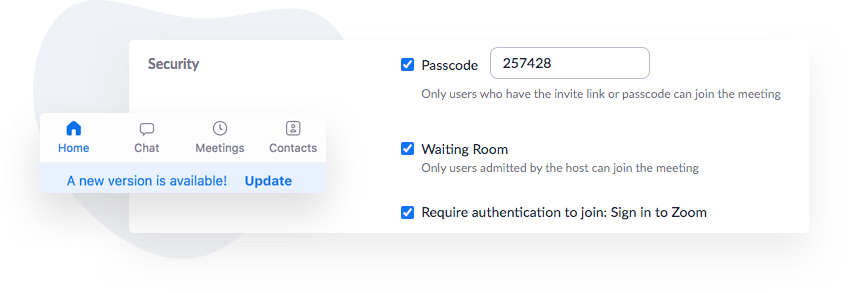
Zoombombing - Perhaps the most widely publicized security issue involved the trend of "Zoombombing" - a catchy name for people logging into Zoom meetings (either uninvited or under an alias) and sharing inappropriate images or messages in the chat box, sharing illicit images or videos using the screen-share function, or unmuting their microphones to say or play inappropriate audio. Zoombombing gained special notoriety because of a variety of incidents during remote education, where young students attending classes were exposed to inappropriate content while teachers looked on helplessly.
Encryption/Data Routing Concerns - Similarly troubling were early revelations that sensitive Zoom meetings might be routed through unsecured servers. Without end-to-end encryption (which Zoom now offers thanks to the uproar surrounding this issue), people were able to easily access private information of users in meetings, as well as content from the meetings themselves.
Vulnerabilities for Phishing/Hacking - Over the course of the year, numerous security weaknesses (from fabricated GIFs to issues with meeting recordings saved in the cloud) have forced Zoom to constantly push new security updates to close loopholes and protect user privacy. While the gaping security concerns that emerged earlier in the year seem to be well in the past, the continued emergence of small loopholes that allow phishing and hacking opportunities only reinforce the need for a dedicated focus on using meeting controls and privacy features to ensure your virtual meetings are protected.

While privacy is a real concern when using Zoom, the good news is that Zoom has rolled out a ton of useful updates and privacy/security controls that can prevent 99% of the issues that we noted above. The trick for users is to know which tools are essential to prevent potential security issues, and which steps you should take when creating and setting up your meeting to protect yourself and your meeting attendees.
It's also important to remember that free Zoom accounts do not offer many of the more enhanced and useful privacy features. You need to pay for a monthly Pro (or higher) account to gain full access to different privacy and security features that can truly protect your meetings.
With that in mind, here are ten essential steps to host a secure Zoom meeting:
Aside from the security and privacy features Zoom offers, there are also some practical steps you can take to ensure digital safety for yourself and your guests:Use an event management platform - The best event management platforms can offer you pre-emptive security features (like secure online invitations, guestlist management, and more) that can help you manage your Zoom event attendees and lower the risk of any uninvited guests before you even start your meeting.
Communicate expectations and rules with guests clearly - While you don't need to lecture a small group of trusted co-workers, if you are hosting a Zoom event with hundreds of attendees you may not know, putting together a digital etiquette reminder email and sending it out to attendees beforehand can help prevent unintentional tech issues to help the meeting run more smoothly.
Gather feedback and learnings to make your next event more smooth - While some guests may be frustrated by overly protective security controls, one of the best ways to strike a balance between security and guest experience is to gather feedback. Find out from your guests if there are certain disabled features they'd appreciate in future meetings, and tailor your event security protocols accordingly!
About the Author

May 28, 2026

May 20, 2026
May 19, 2026
May 11, 2026
Get the latest product updates, event planning tips, and industry insights — straight to your inbox.
You can unsubscribe at any time. Your email will only be used to send RSVPify updates and will never be shared.